Obsolete:Role overrides revisited
Originally the user capabilities were calculated as a sum of role capabilities/overrides in all parent contexts. In 1.9 it was completely rewritten.
Summary of problems in 1.9.x
- overrides in one role affect evaluation of resulting capabilities from other roles
- very hard to explain to normal people (including most of the developers, sorry)
- relies heavily on PHP code and is nearly impossible to optimise with SQL especially when fetching list of courses where user is participating
Proposed solution
Change evaluation algorithm, instead of aggregation caps from all roles in each step, calculate resulting capability for each role and use OR logical operation on the result. The prohibit would work the same way as before.
Example
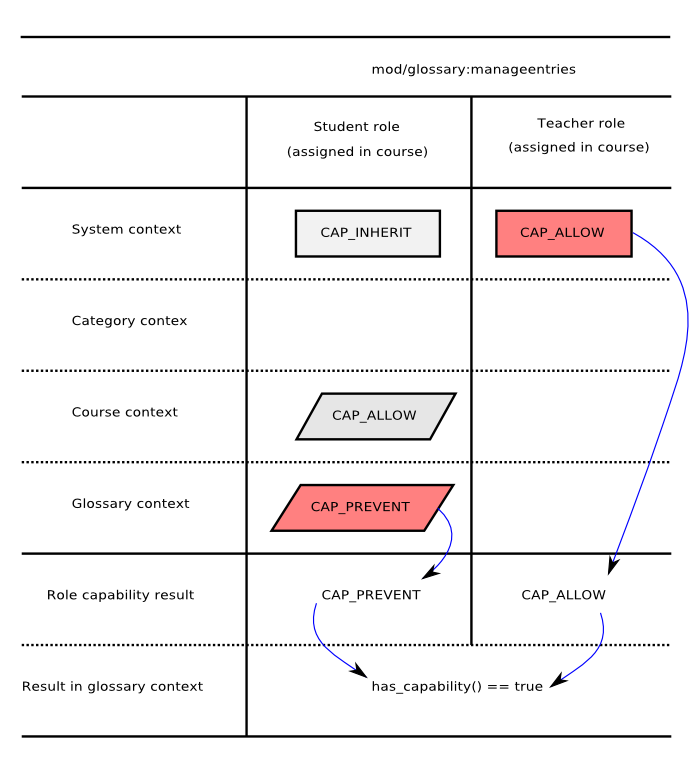
Image above shows an example where one user is both student and teacher in the same course. The override in student role does not affect default capability from default role.
Algorithm
Question: am I allowed to do something in specified context?
- Look up all roles I have in specified context by looking for all my role assignments in parent contexts.
- Is there any CAP_PROHIBIT specified in any role capability or role override? If yes, answer is I can not do that.
- For each role separately find the override or cap definition at the lowest level - this is the result for individual role at this context (CAP_ALLOW, CAP_PREVENT or nothing).
- If at least one role has CAP_ALLOW result I can do it, yay!